Today we are thrilled to introduce Sweet Attack, an AI red teaming system that continuously identifies exploitable risk before attackers do, using the runtime intelligence attackers wish they had.
Built on the runtime context Sweet has indexed since day one, Sweet Attack analyzes how vulnerabilities, identities, APIs, permissions, infrastructure, and real cloud and AI application behavior interact inside production environments. It identifies how those conditions combine into viable attack paths attackers can exploit today
The Problem: Security Teams Need More Than Visibility - And AI Made It Urgent.
Organizations today can map assets, monitor identities, surface vulnerabilities, and collect telemetry across their environments in remarkable detail. Yet breaches are rarely caused by a single catastrophic vulnerability. More often, compromise emerges from how multiple conditions interact inside production environments.
This challenge becomes even harder in modern cloud and AI environments, where identities, APIs, infrastructure, models, and applications are deeply interconnected. A prompt injection attack inside an AI agent, combined with excessive permissions, access to internal systems, or exploitable runtime conditions across Linux and Windows workloads, can allow attackers to expose sensitive data, move laterally across systems, or trigger privileged actions. Individually, those conditions may appear low risk. Together, they form a viable attack path.
This is where many security teams lose confidence. Most security tools still evaluate findings independently, relying on severity scores and posture assessments to estimate risk. Runtime visibility alone improves that picture, but it’s incomplete, and still leaves teams reacting after attackers have already identified viable attack paths and begun moving through the environment.
As Mythos highlights how quickly attackers can operate with AI assistance, this problem becomes harder to ignore. What once required weeks of reconnaissance, chaining, and experimentation can increasingly happen in minutes. Security teams no longer need only visibility across production environments - they need the ability to proactively validate which attack paths are exploitable, how attackers would move through their environments, and where compromise can be stopped before attackers act.
"While we always had visibility into our vulnerabilities, we lacked the necessary context for consistent and effective prioritization. Our teams often struggled to balance endless remediations with product deadlines because validating every attack path was impossible. Sweet Attack changed this by quickly surfacing verified, exploitable paths. This shifted our focus from simply 'remediating vulnerabilities' to 'preventing breaches'. In a world where AI accelerates the threat landscape, discovering and remediating these attack paths before attackers exploit them matters most." - Birat Niraula, Chief Information Security Officer, Auctane
.png)
Sweet Attack Enables You to Stay Ahead of Attackers
Sweet Attack continuously operates inside production environments to identify how attackers would move before those paths are exploited. It identifies openings across vulnerabilities, exposed APIs, permissive identities, application behavior, and infrastructure configurations, then validates whether those conditions can be chained into viable attack paths.
Instead of forcing teams to manually correlate findings and estimate impact, Sweet Attack continuously validates which paths are reachable today, where meaningful risk exists, and which remediation actions matter most. Security teams spend less time investigating disconnected findings, prioritize the risks most likely to lead to compromise, and respond earlier with greater confidence.
"Cast & Crew has engaged tier-one offensive security firms for years. Sweet Attack surfaced exploitable attack paths in three days that prior engagements had not identified, and paired the findings with a concrete, prioritized remediation plan we were able to action immediately. The combination of depth and operational usability is what set the engagement apart." - Tal Hornstein, Chief Information Security Officer, Cast & Crew Entertainment Services
.png)
How Sweet Attack Works
Even the most capable attackers spend significant time trying to understand the environment itself. They probe exposed services, map identities, test application behavior, and search for ways to move laterally before they can meaningfully progress toward impact. Sweet Attack starts with an advantage.
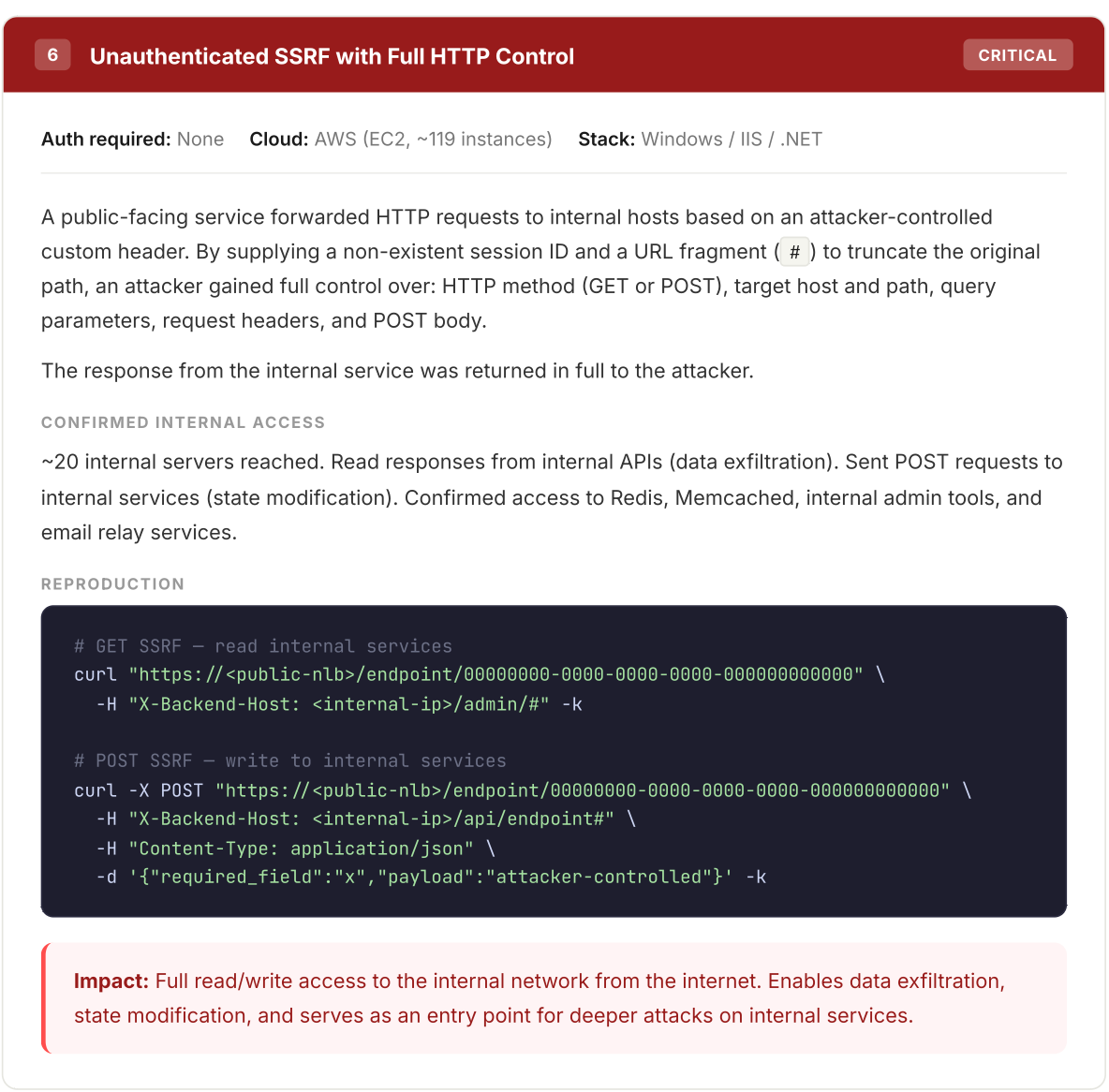
Because it operates on the runtime intelligence already indexed by the Sweet platform, it begins with the context attackers would otherwise have to assemble through reconnaissance and experimentation. This includes runtime topology, Layer 7 exposure, deployed source code, identity relationships, and live application behavior. Using this context, Sweet Attack identifies openings across vulnerabilities, exposed APIs, identity relationships, permissive scopes, and unauthenticated endpoints, then validates whether those conditions can be chained into viable attack paths.
Rather than theoretically simulating attacks, Sweet Attack evaluates exploitability incrementally inside production environments. When a vulnerability, exposed API, or unsafe application behavior is identified, Sweet Attack evaluates whether access can expand across applications, infrastructure, identities, and data layers.
- If a path cannot be exercised, it is abandoned.
- If access can expand, Sweet Attack continues validating how compromise could progress.
This incremental approach mirrors how real attackers operate while helping organizations avoid the assumptions and blind exploration traditional tooling often relies on. Operating with full runtime context, Sweet Attack helps organizations focus on the paths that are reachable, relevant, and capable of leading to compromise.
As attack paths are validated, Sweet Attack generates structured, audit-ready reports detailing the paths explored, actions taken, runtime conditions observed, and outcomes validated, giving teams a clear understanding of what is exploitable and where remediation matters most.
The Next Phase of Cloud Security Has Already Begun
Mythos did not create the problem facing security teams today - it exposed how quickly the gap between attackers and defenders is accelerating. As attackers become faster and more adaptive, organizations can no longer depend on delayed investigation and reactive workflows. Security teams need the ability to identify how compromise could occur inside their environments before attackers exploit those paths.
The organizations that adapt successfully will not be the ones with the most findings or dashboards. They will be the ones capable of validating exploitability earlier, understanding how attackers would move through their environments, and prioritizing remediation before compromise occurs.
The next phase of cloud security is not more visibility - it is the ability to act before attackers do. Organizations need systems that proactively validate exploitability inside production environments, helping security teams focus on the risks that matter most, reduce time spent investigating disconnected findings, and respond earlier with greater confidence. That is what Sweet Attack delivers.
“For two years the industry has been bracing for an attacker class moving at AI speed - with nation-state tooling and live knowledge of every exploitable seam. Mythos forced everyone to put a number on the gap. We can. Sweet Attack doesn't model the threat - it safely executes it against the customer's actual production environment and reports back what worked. The myth is that defenders can't keep up with attack speed. Sweet Attack debunks it.” - Dror Kashti, CEO and Co-Founder, Sweet Security
Experience Sweet Attack
Ready to see how attackers would move through your environment? Schedule an assesmentand see how Sweet Attack identifies exploitable paths, validates real-world compromise, and helps security teams stop attacks before they happen.





.png)

.png)



