Custom Policies in Sweet Security’s Cloud Configurations module let you define posture rules based on how your cloud infrastructure is actually designed and operated, not how a generic framework assumes it should be. This ensures that findings are relevant, actionable, and tied directly to how your systems function in practice.
The Challenge of Applying Generic Policies to Unique Environments
Most cloud security programs start with established frameworks like CIS, NIST, and PCI. These frameworks are valuable for establishing a baseline, but they are designed for broad applicability. They assume a standardized architecture, consistent workflows, and uniform risk models.
As systems evolve, those assumptions quickly break down - what starts as a baseline becomes an operational burden.
You’re left managing findings that:
- Flag technically “risky” configurations that are acceptable by design
- Lack the context needed to determine real impact
- Require manual validation before any action can be taken
At the same time, issues tied to internal architecture, deployment patterns, or operational practices often go undetected because they fall outside predefined rules. The result is a disconnect between what your tools report and what actually requires attention.
Turning Your Environment into Enforceable Policy
Custom Policies allow you to define rules based on how your systems are intended to operate. Instead of relying only on predefined checks, you can encode architectural decisions, ownership boundaries, and operational standards directly into your security posture.
This changes how findings are generated. Expected configurations are no longer flagged unnecessarily, while deviations from intended behavior are consistently surfaced, and the result is a more focused and reliable set of findings.
Creating Custom Policies in the Sweet Platform
Sweet enables custom policy creation in two ways:
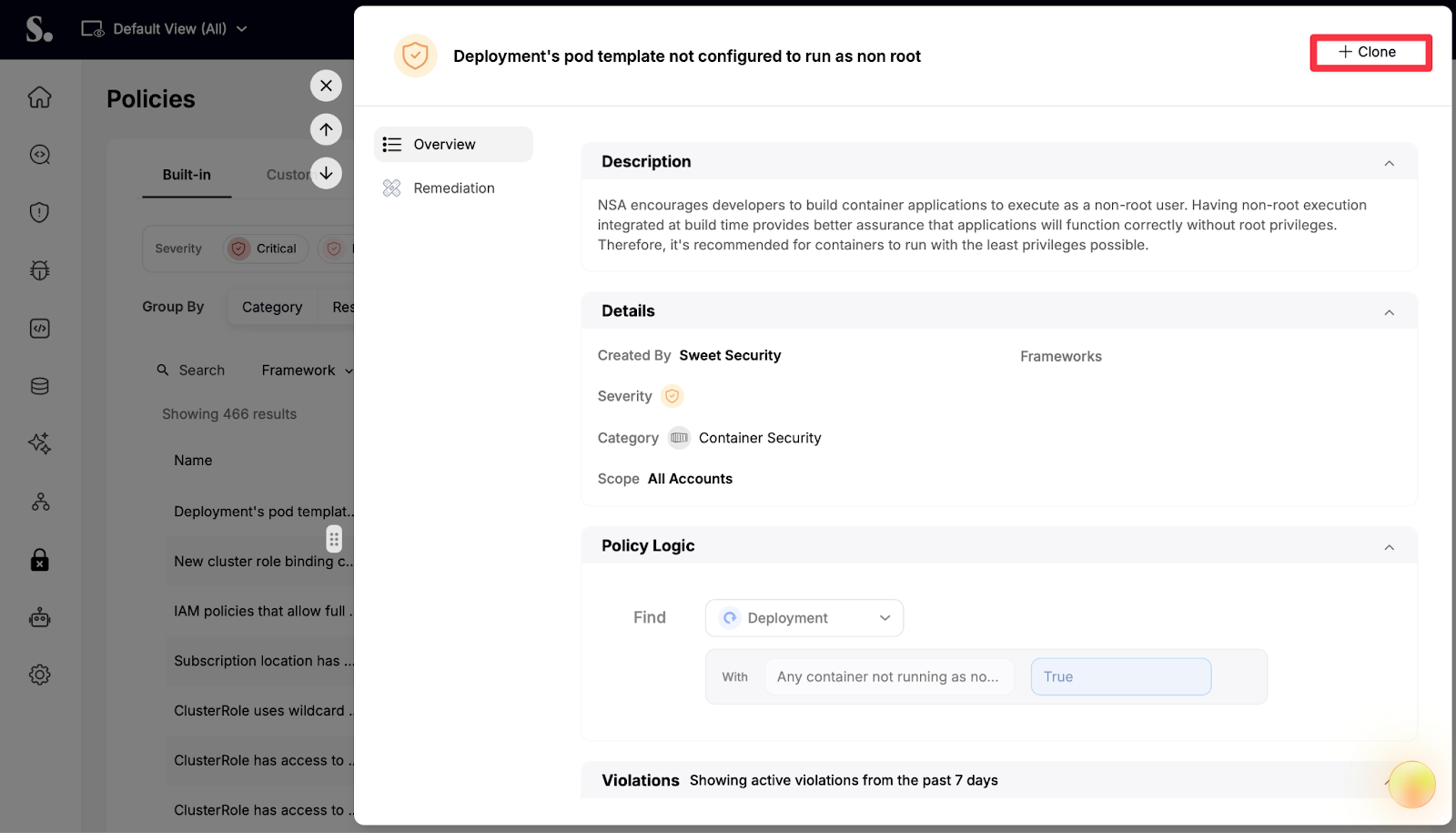
1. If a built-in policy is close to your requirements, it can be cloned directly from the Policies screen. The policy logic is visible and pre-populated, allowing you to modify conditions, scope, and severity without starting from scratch.
2. Policies can also be created from the ground up using the Query Builder. You select a resource type, define conditions based on resource properties, and combine filters using logical operators to match specific criteria.

Before saving, policies can be tested against your live environment to ensure they identify the intended resources.
Improving Signal Quality with Context-Aware Custom Policies
Custom Policies ensure that only meaningful violations are generated. Instead of filtering alerts after they appear, you define upfront which configurations should be considered violations. This makes detection more intentional and reduces unnecessary triage.
Each policy within the Sweet Platform includes context such as severity, category, and remediation guidance, so when a violation occurs, it can be understood and addressed immediately. In addition, Sweet continuously evaluates policies, and matching resources are surfaced in real time.
By defining risk based on how your systems are actually configured and used, findings the Sweet Platform become more accurate and require less validation. Teams can focus on resolving issues with real impact, rather than determining whether an alert is relevant.
Learn More
To learn more about Custom Policies in Sweet Security or to see how they can be applied to your environment, schedule a customized demo with our team.




.png)

.png)




