There's a meeting most Application Security Engineers know well. You walk into a sprint planning session, Jira ticket in hand, armed with a CVE ID, a severity score, and a one-line recommendation: upgrade package X. The engineering lead looks up and asks, "To which version? And what else breaks if we do?" You don't have a great answer. The meeting moves on. The ticket stays open.
This is not a people problem; It's an information problem. And it's one we set out to fix.
The Difference Between Noise and Real Risk
A golang.org/x/crypto package, a direct dependency explicitly imported for password hashing, flagged with CVE-2024-45337, an authentication bypass with a base score of 9.1. Already critical on paper. The Sweet Score pushes it to 9.9: the package is actively loaded, inbound connections observed, exploitation probability in the wild very high. This isn't theoretical - it's a confirmed, active exposure.
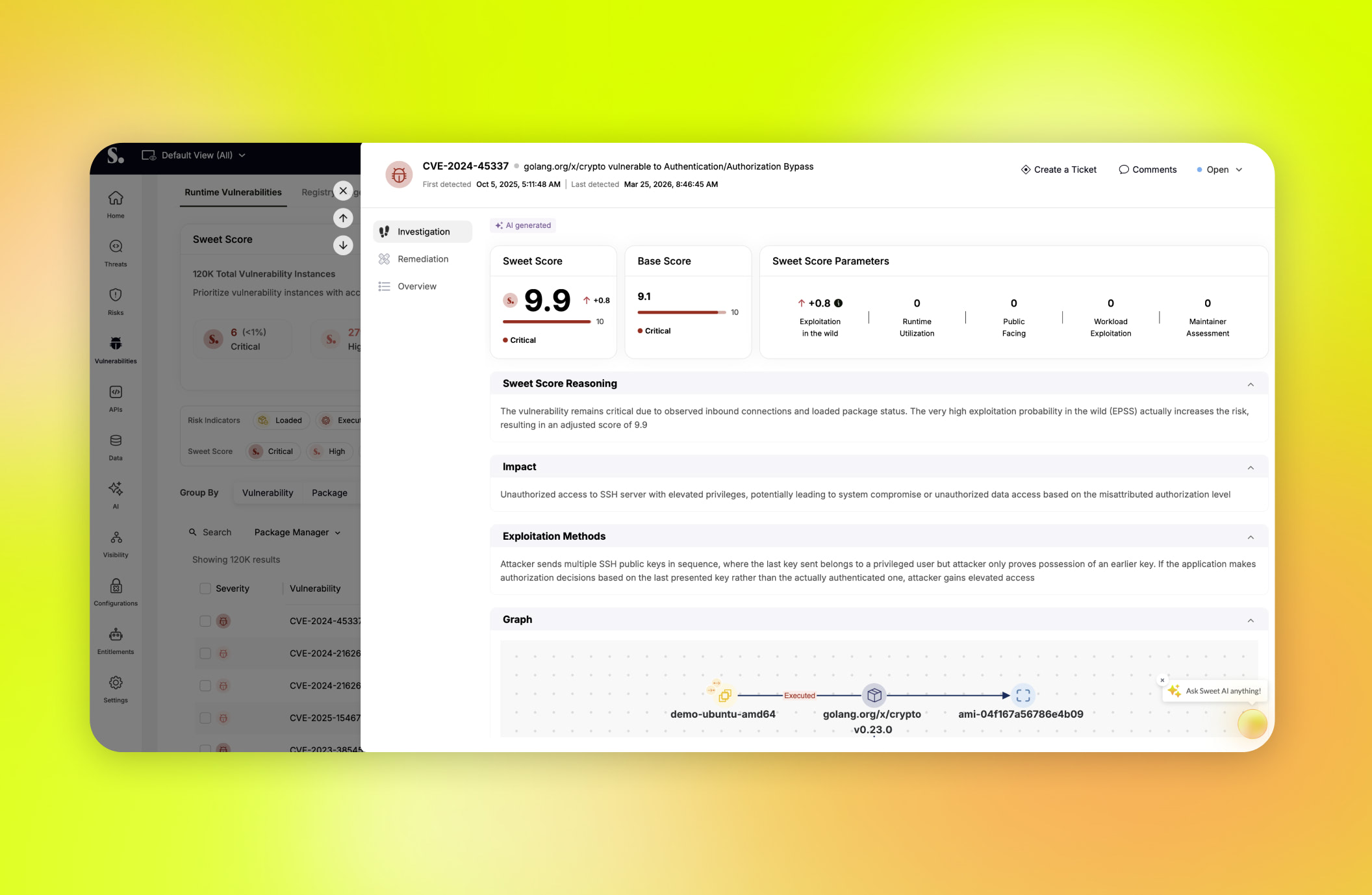
Not every critical CVE is critical in your environment. When the Sweet Score confirms this one is, you have the evidence to act and the confidence to bring engineering along. But here's where things used to fall apart: multiple tickets, same package, each pointing vaguely at an upgrade. The developer asks the obvious question - "Which version do I upgrade to?" - and the answer was never clean.
Consolidated Remediation: One Package, One Decision
Sweet's consolidated remediation changes this entirely. Instead of isolated CVEs, you see the full picture - every vulnerability affecting the package, unified in a single view. Sweet surfaces up to five available upgrade versions, each with a complete breakdown:
- Which vulnerabilities get fixed
- Which remain
- Whether any new vulnerabilities are introduced by the upgrade itself
The recommended version is automatically highlighted — the one that resolves the most vulnerabilities while introducing the fewest new ones. It's not a gut call. It's a calculated recommendation based on the full vulnerability landscape across the version spectrum.
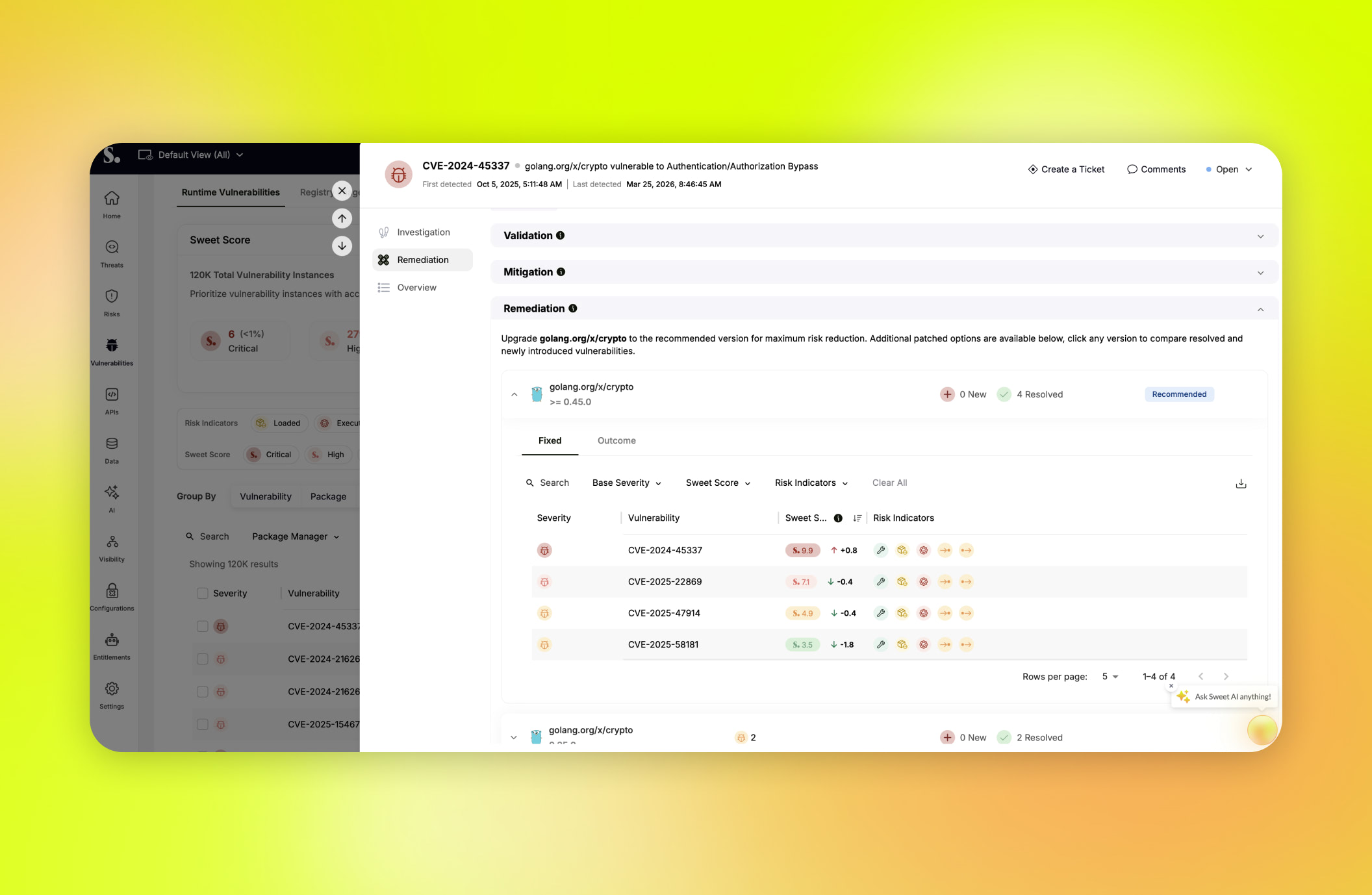
The security engineer walks into sprint planning differently now. Not with a stack of CVE IDs, but with: "Upgrade golang.org/x/crypto to version X. Here's why it's urgent — actively loaded, inbound connections observed, high exploitation probability. Here's what it fixes — all critical CVEs. Here's what it doesn't break - nothing new introduced."
The developer can review the full before-and-after in the platform, ask informed questions, and get to work. No back-and-forth. No ambiguity.
Closing the Gap Between Finding and Fixing
Application security shouldn't be a constant stream of alerts to triage, but a clear path from detection to resolution. When prioritization and remediation actually connect, security stops slowing teams down and starts moving at the same pace as business. That philosophy is part of Sweet's broader approach to Application Security, built around the belief that a finding is only useful if it's actionable.
Our Sweet Score shows you what truly matters in your environment, and consolidated Remediation shows you exactly what to do next - with clarity, context, and confidence. Together, they turn what used to be noisy, fragmented signals into fast, informed decisions your team can execute on.
If you’re tired of chasing CVEs and want to see what it looks like when everything just clicks, we’d love to show you. Request a customized demo and see how your team can go from noise to decision in minutes.

.jpg)